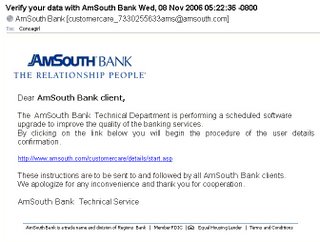
For the past few weeks, many people have been "leaving me song downloads on MySpace", but now I'm getting vacation photos from Bob, Anthony, Henry, Sally, Donald, etc.
It was interesting that I do know an Anthony who is on vacation and so the message below caught my attention:
Anthony has sent you a photo from Vacation!
Click here to view the photo Anthony has sent from vacation:
http://xxxxxxx
Click here to share your photos with a friend:
http://xxxxxxx
----------------------
At Vacation Photos Online we care about your privacy. We have sent you this
notification to facilitate your use as a member of our service. If
you don't want to receive emails like this to your email account
in the future, please click below:
http://xxxxxxxx
Vacation Photos Online Inc. - 4598 River Glen Dr, Las Vegas, NV 89103 USA
©2006 VP Online Inc., All Rights Reserved.
o 3Com 3C507 Etherlink 16/TP
2.1.2. Ethernet cards
The goal of the new ports collection is to make each port as `plug-
10.4.12. * PCMCIA
0xd4 write Single Mask Register Bit
... much more junk deleted here ....
The links in this email were within the tarx.net domain. The Whois information for this domain includes:
Domain name: TARRX.NET
Registrar: PacNames
Referral URL: http://www.pacnames.com/
Domain Registrant: TOTALNIC-128733 (XSALSA@GMAIL.COM)
Alex Rodrigez
Alex Rodrigez
PO box 109 WP 1432
Lappeenranta NA 53101
FI
Telephone: +358.207818027
Fax: +358.207818027
...
Domain creaton date: 2006-11-07 17:15:00.0
Domain expiration date: 2007-11-07 22:34:13.0
Which is pretty much the same information returned for mp3shest.com (the target site for the myspace.com attack I wrote about earlier). It's also the same info for several other domains received with this and they myspace attack including: gromko-oem.com, gromko-oem.net, mp3vosem.com, etc.
I followed the link in a fairly safe environment to a page that was offering to sell common software packages at like 10 cents on the dollar. Clearly a deal that's too good to be true.
I'm not sure whether this is simply plain old SPAM trying to get you to buy their stuff, a SCAM trying to get you to pay for something you aren't really going to get (the fact that thesoftwaree they are selling is only available via download) or, much more likely if you ask me, an attempt to get your credit card information to use for other identity theft related attacks.
UPDATE: 11/26 - today he started using a new domain that was registered Thanksgiving day (11/23): luk-soft.net
UPDATE: 11/28 - He just won't quit -- today he registered two more domains and has started using them for this scam: hlopai-oem.net and hlopai-oem.com
UPDATE: 11/30 - In another offer for vacation photos, the domain was tarrx.com (as opposed to the former tarx.net) and this time the domain was owned by:
Registrant:
Wan-Fu China, Ltd. (TARRX-COM-DOM)
P.O.Box CB-11901
Nassau,
BS
+32.70426163
+32.70426163
business@wanfuchina.com
Domain Name: TARRX.COM
Status: PROTECTED
..... duplicate info cut out here .....
Record last updated on 27-Nov-2006.
Record expires on 26-Nov-2007.
Record created on 26-Nov-2006.
That site just throws up pop-up adds at you. I'm not sure if it's the same person doing this attack or is this another person using the same attack to get revenue from pushing pop-up adds.
In any case, beware... don't click on or follow links in these emails.
UPDATE: 12/20 - this attack seems to have picked up again given the junk in my inbox as well as the hits on this page. New domains being used include: ding-dong-oem.com, txrp.tuhloem.com (which is also used in another attack I wrote about), hlopai-oem.net, etc.
Tags :
identity
/ identity theft
/ spam
/ scam
/ myspace
/ vacation